I recently read that SSH keys provide a secure way of logging into a Linux and Unix-based server. How do I set up SSH keys on a Linux or Unix based systems? In SSH for Linux/Unix, how do I set up public key authentication?
This page explains a public key and shows you how to set up SSH keys on a Linux or Unix-like server. I am assuming that you are using Linux or Unix-like server and client with the following software:
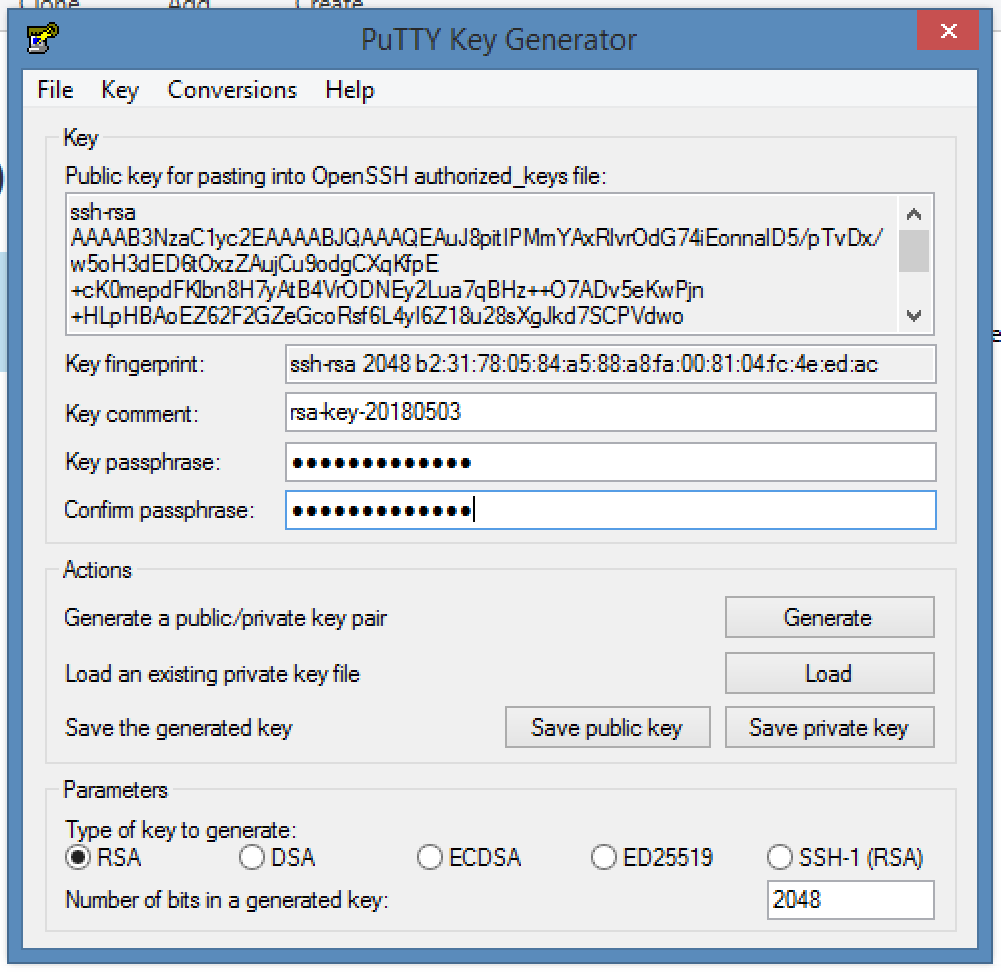
Jun 22, 2012 SSH keys provide a more secure way of logging into a virtual private server with SSH than using a password alone. With SSH keys, users can log into a server without a password. This tutorial explains how to generate, use, and upload an SSH Key Pair. This will create a RSA public/private key pair in the.ssh directory below your account’s home directory. Public key file name: idrsa.pub Windows does not ship with software for generating SSH keys. Although many third party software packages can be used, this Lab Step uses PuTTYgen to generate SSH keys. Installation of SSH Keys on Linux - A Step-By-Step Guide. Outlined below is a step-by-step guide detailing the process of installing SSH Keys on a Linux server: Step One: Creation of the RSA Key Pair. The first step in the installation process is to create the key pair on the client machine, which would, more often than not, be your own system.
- OpenSSH SSHD server
- OpenSSH ssh client and friends on Linux (Ubuntu, Debian, {Free,Open,Net}BSD, RHEL, CentOS, MacOS/OSX, AIX, HP-UX and co).
What is a public key authentication?
OpenSSH server supports various authentication schema. The two most popular are as follows:
- Passwords based authentication
- Public key based authentication. It is an alternative security method to using passwords. This method is recommended on a VPS, cloud, dedicated or even home based server.
How to set up SSH keys
Steps to setup secure ssh keys:
- Create the ssh key pair using ssh-keygen command.
- Copy and install the public ssh key using ssh-copy-id command on a Linux or Unix server.
- Add yourself to sudo or wheel group admin account.
- Disable the password login for root account.
- Test your password less ssh keys login using ssh user@server-name command.
Let us see all steps in details.
How do I set up public key authentication?
You must generate both a public and a private key pair. For example:
Where,
- server1.cyberciti.biz – You store your public key on the remote hosts and you have an accounts on this Linux/Unix based server.
- client1.cyberciti.biz – Your private key stays on the desktop/laptop/ computer (or local server) you use to connect to server1.cyberciti.biz server. Do not share or give your private file to anyone.
In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords. Feel free to replace server1.cyberciti.biz and client1.cyberciti.biz names with your actual setup. Enough talk, let’s set up public key authentication. Open the Terminal and type following commands if .ssh directory does not exists:
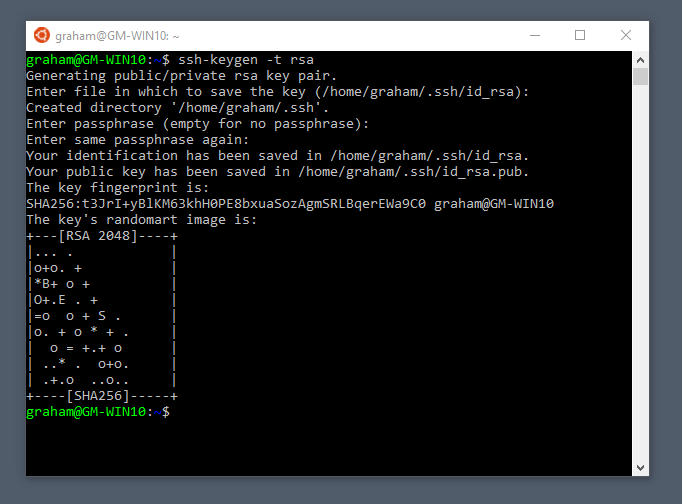
1: Create the key pair
On the computer (such as client1.cyberciti.biz), generate a key pair for the protocol.
Sample outputs:
You need to set the Key Pair location and name. I recommend you use the default location if you do not yet have another key there, for example: $HOME/.ssh/id_rsa. You will be prompted to supply a passphrase (password) for your private key. I suggest that you setup a passphrase when prompted. You should see two new files in $HOME/.ssh/ directory:
- $HOME/.ssh/id_rsa– contains your private key.
- $HOME/.ssh/id_rsa.pub – contain your public key.
Optional syntax for advance users
Generate Rsa Key Pair Linux Download
The following syntax specifies the 4096 of bits in the RSA key to creation (default 2048):$ ssh-keygen -t rsa -b 4096 -f ~/.ssh/vps-cloud.web-server.key -C 'My web-server key'
Where,
- -t rsa : Specifies the type of key to create. The possible values are “rsa1” for protocol version 1 and “dsa”, “ecdsa”, “ed25519”, or “rsa” for protocol version 2.
- -b 4096 : Specifies the number of bits in the key to create
- -f ~/.ssh/vps-cloud.web-server.key : Specifies the filename of the key file.
- -C 'My web-server key' : Set a new comment.
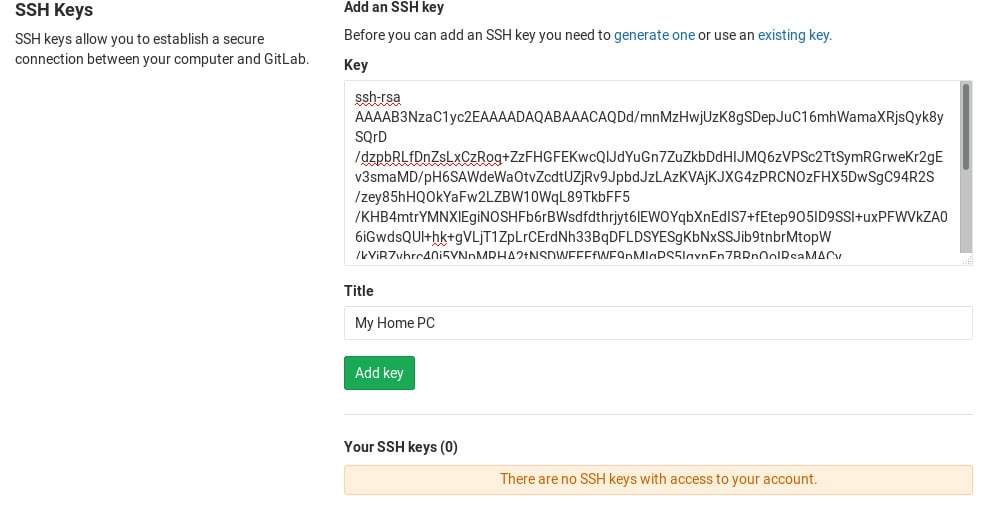
2: Install the public key in remote server
Use scp or ssh-copy-id command to copy your public key file (e.g., $HOME/.ssh/id_rsa.pub) to your account on the remote server/host (e.g., nixcraft@server1.cyberciti.biz). To do so, enter the following command on your client1.cyberciti.biz:
OR just copy the public key in remote server as authorized_keys in ~/.ssh/ directory:
A note about appending the public key in remote server
On some system ssh-copy-id command may not be installed, so use the following commands (when prompted provide the password for remote user account called vivek) to install and append the public key:
3: Test it (type command on client1.cyberciti.biz)
The syntax is as follows for the ssh command:
Or copy a text file called foo.txt:
You will be prompted for a passphrase. To get rid of passphrase whenever you log in the remote host, try ssh-agent and ssh-add commands.
What are ssh-agent and ssh-add, and how do I use them?
To get rid of a passphrase for the current session, add a passphrase to ssh-agent and you will not be prompted for it when using ssh or scp/sftp/rsync to connect to hosts with your public key. The syntax is as follows:
Type the ssh-add command to prompt the user for a private key passphrase and adds it to the list maintained by ssh-agent command:
Enter your private key passphrase. Now try again to log into user@server1.cyberciti.biz and you will not be prompted for a password:
One can list public key parameters of all identities with the -L option:ssh-add -L
Deleting all private keys from the ssh-agent can be done with the -D option as follows:ssh-add -D
When you log out kill the ssh agent, run:kill $SSH_AGENT_PID
You can also add something like the below to your shell startup to kill ssh-agent at logout:trap 'kill $SSH_AGENT_PID' 0
4: Disable the password based login on a server
Login to your server, type:
Edit /etc/ssh/sshd_config on server1.cyberciti.biz using a text editor such as nano or vim:
Warning: Make sure you add yourself to sudoers files. Otherwise you will not able to login as root later on. See “How To Add, Delete, and Grant Sudo Privileges to Users on a FreeBSD Server” for more info.
$ sudo vim /etc/ssh/sshd_config
OR directly jump to PermitRootLogin line using a vim text editor:$ sudo vim +/PermitRootLogin /etc/ssh/sshd_config
Find PermitRootLogin and set it as follows:
Save and close the file. I am going to add a user named vivek to sudoers on Ubuntu Linux:# adduser vivek
Finally, reload/restart the sshd server, type command as per your Linux/Unix version:
5: How to add or replace a passphrase for an existing private key?
To to change your passphrase type the following command:ssh-keygen -p
6: How do I backup an existing private/public key?
Just copy files to your backup server or external USB pen/hard drive:
How do I protect my ssh keys?
- Always use a strong passphrase.
- Do not share your private keys anywhere online or store in insecure cloud storage.
- Restrict privileges of the account.
How do I create and setup an OpenSSH config file to create shortcuts for servers I frequently access?
See how to create and use an OpenSSH ssh_config file for more info.
Conclusion
This page explained how to set up ssh keys for authentication purposes. For more info see the following resources:
- Man pages – ssh-keygen(1)
- OpenSSH project homepage here.
And, there you have it, ssh set up with public key based authentication for Linux or Unix-like systems.
ADVERTISEMENTS
While Encrypting a File with a Password from the Command Line using OpenSSLis very useful in its own right, the real power of the OpenSSL library is itsability to support the use of public key cryptograph for encrypting orvalidating data in an unattended manner (where the password is not required toencrypt) is done with public keys.
The Commands to Run
Generate a 2048 bit RSA Key
You can generate a public and private RSA key pair like this:
openssl genrsa -des3 -out private.pem 2048
That generates a 2048-bit RSA key pair, encrypts them with a password you provideand writes them to a file. You need to next extract the public key file. You willuse this, for instance, on your web server to encrypt content so that it canonly be read with the private key.
Export the RSA Public Key to a File
Generate Rsa Key Pair Linux Openssl
This is a command that is
openssl rsa -in private.pem -outform PEM -pubout -out public.pem
The -pubout flag is really important. Be sure to include it.
Next open the public.pem and ensure that it starts with-----BEGIN PUBLIC KEY-----. This is how you know that this file is thepublic key of the pair and not a private key.
Generate Rsa Key Linux
To check the file from the command line you can use the less command, like this:
less public.pem
Do Not Run This, it Exports the Private Key
A previous version of the post gave this example in error.
openssl rsa -in private.pem -out private_unencrypted.pem -outform PEM
The error is that the -pubout was dropped from the end of the command.That changes the meaning of the command from that of exporting the public keyto exporting the private key outside of its encrypted wrapper. Inspecting theoutput file, in this case private_unencrypted.pem clearly shows that the keyis a RSA private key as it starts with -----BEGIN RSA PRIVATE KEY-----.
Visually Inspect Your Key Files
It is important to visually inspect you private and public key files to makesure that they are what you expect. OpenSSL will clearly explain the nature ofthe key block with a -----BEGIN RSA PRIVATE KEY----- or -----BEGIN PUBLIC KEY-----.
You can use less to inspect each of your two files in turn:
less private.pemto verify that it starts with a-----BEGIN RSA PRIVATE KEY-----less public.pemto verify that it starts with a-----BEGIN PUBLIC KEY-----
The next section shows a full example of what each key file should look like.
The Generated Key Files
The generated files are base64-encoded encryption keys in plain text format.If you select a password for your private key, its file will be encrypted withyour password. Be sure to remember this password or the key pair becomes useless.
Java Generate Rsa Key Pair
The private.pem file looks something like this:
Create Rsa Key Linux
The public key, public.pem, file looks like:
Protecting Your Keys
Depending on the nature of the information you will protect, it’s important tokeep the private key backed up and secret. The public key can be distributedanywhere or embedded in your web application scripts, such as in your PHP,Ruby, or other scripts. Again, backup your keys!
Remember, if the key goes away the data encrypted to it is gone. Keeping aprinted copy of the key material in a sealed envelope in a bank safety depositbox is a good way to protect important keys against loss due to fire or harddrive failure.
Oh, and one last thing.
If you, dear reader, were planning any funny business with the private key that I have just published here. Know that they were made especially for this series of blog posts. I do not use them for anything else.
Found an issue?
Generate Rsa Key Pair Linux Software
Rietta plans, develops, and maintains applications.
Learn more about our services or drop us your email and we'll e-mail you back.